As we increasingly embrace cloud-based applications for our daily work, requirements for managing security are changing at both a personal and organizational level. Central to the conversation of online security is that of identity and access control.
Consumers of social sites like Google, Facebook and Microsoft already recognize the benefits of having a centralized identity. Signing into a dozen sites with a single account means you have a dozen less passwords to remember... and have compromised.
Organizations face unique challenges as they work to secure the vast array of online services their employees wish to use, including Recollective.
To meet this need, Recollective has integrated support for multiple enterprise-grade identity providers. These integrations improve security, simplify site access and streamline the onboarding of new panelists and administrators.
Integrations options have been added for Okta, a leading identity platform, and OpenID Connect (OIDC), an open source protocol for federated identities. Our existing integrations to Google and Facebook have also been completely redeveloped to centralize and streamline the configuration of identity providers.

What is an Identity Provider?
An identity provider (IdP) stores and manages a user's digital identity. It acts as an approved list of people permitted to access a given set of applications. An IdP takes care of validating that a visitor to a site is who they claim to be, without having the application store sensitive credentials or outdated information. Once integrated, an IdP provides a "single sign-on" experience which benefits both the end user and the organization.
For example, when an e-commerce website prompts its users to sign in with their Google account, Google is acting as the identity provider. The end user does not need to create a password at the online store.
The two main types of identity providers are social and enterprise. Social identity providers are consumer-grade service providers like Google, Facebook and Microsoft. An enterprise identity provider is typically a private service used for identity and access management (IAM) and aims to authenticate users for online activities that take place behind a registration wall, such as access to a Recollective site.
An external identity provider is attractive to organizations given its security benefits:
- A central audit trail of all access events, which makes it easier to prove who is accessing what resources and when.
- Ease with which one can provision and de-provision user accounts across dozens of services.
- Reduced password fatigue by ensuring users can skip the creation and maintenance of passwords. Fatigue leads to password reuse and other habits that weaken password security.
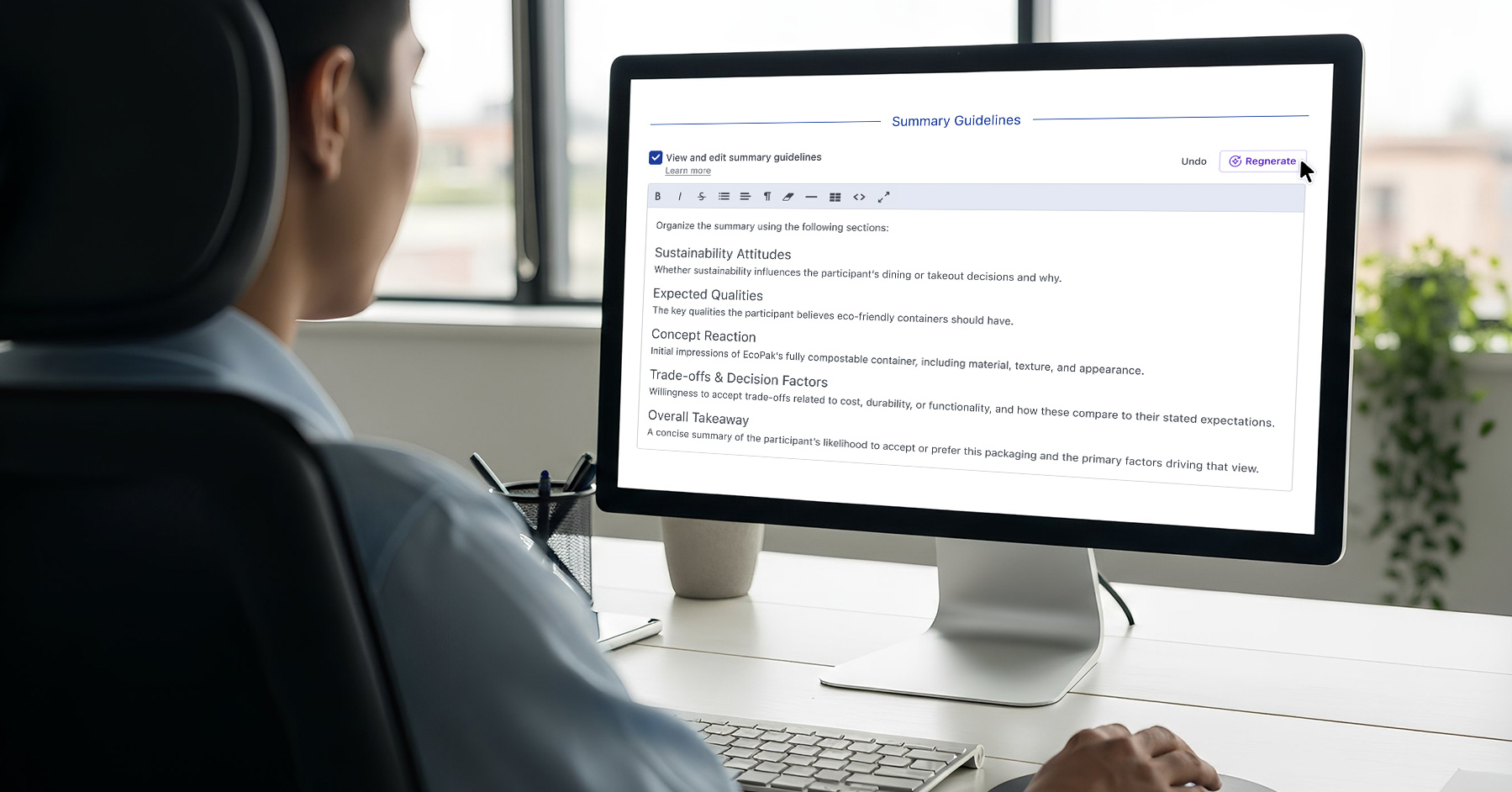
Setup & Configuration
Access to these new identity provider integrations in Recollective requires the purchase of a Single Sign-On (SSO) option.
Even before SSO is enabled, a site can begin configuring multiple identity providers. Each provider can be exposed to one or more user roles (i.e. Analysts, Moderators, Clients and/or Panelists) and be assigned a custom label and colour.

The following identity providers are currently supported:
- Okta
- OpenID Connect (OIDC)

Okta
- Okta is a leading identity platform with over 13,000 customers worldwide.
- Recollective is an Okta Verified integration and appears in the Okta Integration Marketplace (OIN).
- Once an Okta admin grants access to Recollective, end users will have Recollective listed among their approved applications. Selecting Recollective from the Okta dashboard can instantly provision a new Recollective account.

OpenID Connect
- OpenID Connect (OIDC) is an authentication protocol based on the OAuth 2.0 family of specifications.
- OIDC is the underlying protocol that powers many social sign-in options like Google, Facebook and others.
- The OIDC protocol is overseen by the non-profit OpenID Foundation.
- Google is unique as it offers both a consumer service (Gmail) as well as an enterprise solution (Google Workspace).
- The Google integration in Recollective functions with both the consumer and enterprise services.
- Multiple Google integrations can be added to a single Recollective site and each can be restricted to select user roles. One instance could be for panelists that sign-in with Gmail accounts, while another is restricted to a specific Google Workspace domain.
- To enable the automatic provisioning of administrative accounts via Google, Recollective requires a domain restriction be configured.
- Facebook is a social service storing and authenticating 2.85 billion active users each month.
- Recollective's integration with Facebook is a great way to streamline the recruitment and onboarding of new panelists.
- Facebook identities can be used by administrators but it cannot be configured to provision new administrative accounts.
User Experience
Once identity providers are configured for a Recollective site, a number of key areas will be updated to create a streamlined user experience:
Login
- In addition to setting up identity providers, Recollective administrators can now disable the use of password authentication for one or more user roles. If disabled, users of that role must use an external identity provider to access the site.
- Identity providers available to panelists will appear immediately on the login form.

- Identity providers limited to administrative roles will not appear until an administrator's username or email address is provided on the login form. If preferred, such identity providers can be configured to appear to all site visitors.

- Once an identity provider is used to login, the authenticated user is returned to Recollective, matched to the linked account and signed in.
- When users returns in the future, the identity provider last used will appear immediately to save time.

- If no account in Recollective is linked to an external user account, various account handling options can be configured. Matching existing accounts by email address is an option as well as instantly creating a new Recollective user.
Registration
- When someone is invited to register as a panelists, identity providers enabled for panelists will appear above the registration form. If used to sign in, the registering user will not be asked to define a password for Recollective.
- Administrators that are invited to register for an account will presented with identity providers configured for the user role being created (e.g. Analyst, Moderator or Client).
- When an identity provider is limited to administrative roles, a "Login Link" can also be shared with new admins to ensure they can directly access the identity provider.
Account Settings
- All Recollective account holders can visit their personal Account Settings to manage their identity providers.
- A single account can use multiple providers and be unlinked at any time.

- The use of an identity provider does not prevent Recollective users from enabling two-factor authentication (2FA) nor does it prevent Analysts from mandating the use of 2FA. Two-factor authentication is the use of a second device, like a mobile phone, to generate a one-time code to be provided during the login process which further secure access to the account.
Account Handling Options
When an unauthenticated user accesses a Recollective site, they are challenged to login. If they choose an identity provider and login to that provider successfully, it does not mean they have instant access to the Recollective site.
Rather than deny access to the authenticated but unrecognized visitor, an identity provider integration in Recollective can be configured to help the user securely gain access.

An identity provider can be configured to trust the email address associated to the user. If so, it will seek to match that email address with an existing Recollective account holder. The matching process will be limited to the user roles enabled for the identity provider. If a match is made, the Recollective account will be linked and access will be granted instantly.
If email matching is not enabled, or no match is made, a Recollective identity provider configured for administrators can be permitted to add a new admin account. The user role granted to the new account will be the lowest role enabled for the identity provider. When provisioning Moderator and Client user accounts, default study memberships can also be assigned.
To streamline the onboarding of new administrators, Recollective also provides a "Login Link" for identity providers that are limited to administrative roles. The link can be copied from the identity provider configuration area and shared with new administrators so they are presented with the correct sign-in option upon their first visit.
Getting Started
We're very excited about these new features and our status as an Okta Verified integration. We know that many of our enterprise customers will be happy to learn that they can now centrally manage their Recollective accounts.
Our research agency partners will be excited to learn that they have an entirely new way to onboard their clients. An integration to the client's identity platform will mean that stakeholders can join a Recollective site with ease from a trusted source. No longer will Analysts need to pre-register or invite individual clients.
To learn more about these new capabilities, or to try them out first-hand, please reach out to your account representative or contact us today for a demonstration.





.svg)